Copyright ©2004 Foundstone, Inc. All Rights Reserved »Google Hacking Searching For Ways To Stop Hackers Copyright ©2004 Foundstone, Inc. All Rights Reserved. - ppt download
Adrian Crenshaw. I run Irongeek.com I have an interest in InfoSec education I don't know everything - I'm. - ppt download
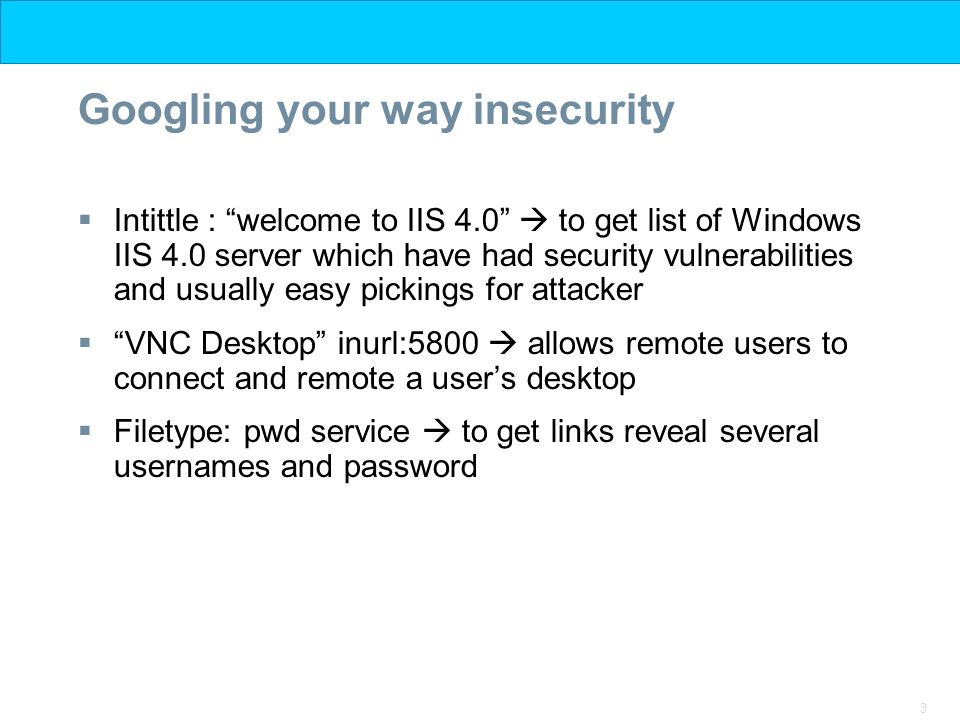
1 Footprinting Scanning Enumeration Isbat Uzzin Nadhori Informatical Engineering PENS-ITS. - ppt download